Network security lecture osi model the osi model groups information



Network Security: Lecture 1
• This lecture covers more details, especially with regard to: Security Concepts and Threats
An overview of the above, with regard to the lower layers of the OSI Network Model. OSI and TCP/IP Models
Reviewing the OSI or TCP/IP models and discussing some security aspects of each of the OSI or TCP/IP layers.
Security Concepts and Threats
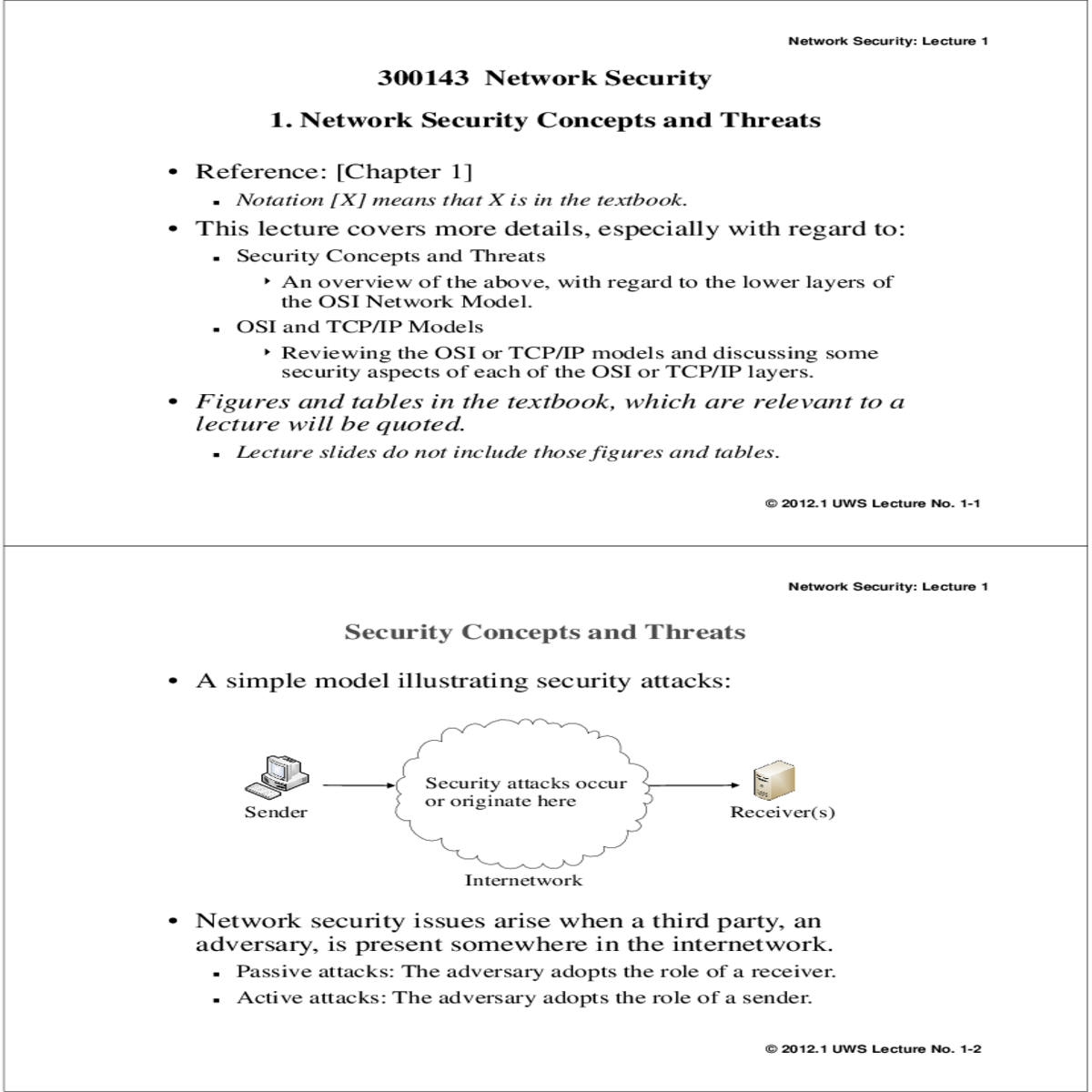
• A simple model illustrating security attacks:
| Sender |
|---|
Active attacks: The adversary adopts the role of a sender.
© 2012.1 UWS Lecture No. 1-2
... Passive Attacks
• Passive attacks mainly involve observing or copying the information being transmitted between the two end entities.• A message being transmitted usually consists of two parts: Message header
Message body
• Two kinds of passive attacks depending on what
information contents are being observed:
Unauthorized release of message contents usually from the message body
Traffic analysis
Observing information about the message, i.e.
Network Security: Lecture 1
Active Attacks …
| Attacker |
|---|
message M
• A spoofing attack may lead to modifying information stored on the target end entity
Message with false contents
... Active Attacks …
• Replay attack
Makes use of a previously sent message from the sender
| Bob | Attacker | |||
|---|---|---|---|---|
|
|
|||
| message 1 | ... | |||
• Modification attack:
An attacker interrupts a message, modifies it, and sends the modified copy to the receiver. Modification attacks also include message stream modification, e.g.
• Denial of service (DoS) attack
Sending bogus or craft messages to a receiver (which can be a computer or a network) to adversely affect its operation. May be classified as:
Asymmetric
• The attacker uses little resource from himself/herself to perform a DoS attack on a larger or more powerful target.
Network Security: Lecture 1
Secure Communication Requirements ...
Alice
Are messages being
eavesdropped?
This includes message stream integrity.
• Message (origin) authentication
The link between the transmitted information and the sender’s identity needs to be verified. Also for non-repudiation purpose.
• The OSI model groups information, functions, and resourses into 7 layers or levels of abstraction.
| Layer No. | Layer Name |
|
|
|---|---|---|---|
In theory. a security attack can occur in any of the layer.
© 2012.1 UWS Lecture No. 1-12
• OSI layer structure is used in most of the discussions regarding different layers of networking
• In the following, some details of the lower 4 layers of the OSI model will be discussed and reviewed with regard to network security.
Information at this level is represented in the form of electrical, optical or electromagnetic waves.
• Attacks at this level are usually passive in nature, e.g. wire- tapping and eavesdropping.
• Physical security and security at the OSI physical layer are
not parts of this unit.
• Information at this layer is encapsulated in frames.
• Frame format (Ethernet):
| Header | Data | |
|---|---|---|
|
||
|
• Passive attack is possible by changing the mode of a NIC to promiscuous mode to capture all the frames transmitted on the LAN.
• Privacy protection:
Router
|
Attacker |
|
|
|---|---|---|---|
192.168.1.1 MAC_PC3
192.168.1.2 MAC_PC2
© 2012.1 UWS Lecture No. 1-17
Network Security: Lecture 1
192.168.1.1 MAC_PC3
PC4’s ARP Cache
Network Security: Lecture 1
Network Layer …
| IP Payload | |
|---|---|
|
|
|
|
Network Security: Lecture 1
… Network Layer
© 2012.1 UWS Lecture No. 1-20



It establishes a communication session between the source and destination first before any data are sent.
© 2012.1 UWS Lecture No. 1-21
Sent in one
message ACK-SYN
SYN
ACK
| SYN | ||
|---|---|---|
| ACK |
© 2012.1 UWS Lecture No. 1-22



Each computer needs to store the state of this process.
At this point, the server
• stores the state of the half-open connection
• waits for the client to send the last ACK message
• If the client does not respond, then the server will drop the half-open connection after a time-out period.
Network Security: Lecture 1
… TCP SYN Flood Attack
Temporary storage for
half-open connections
© 2012.1 UWS Lecture No. 1-24
Passive attacks are side-effects and usually attackers (whether
human or malicious programs) are actively engaged in the attacks.
*** End ***
© 2012.1 UWS Lecture No. 1-25