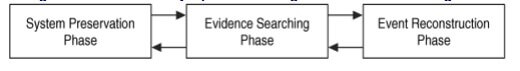
Digital crime scene investigation process
Digital crime scene investigation is divided into three event stages. The process is same for live and dead analysis of the forensic image.
The live analysis is done when operating system and resources are being used in the investigation to find and process evidence. A dead analysis occurs when specialized tools are being used in a specialized operating system to find and process evidence. A true analysis would not be able to recover or recreate the deleted data or hidden data, so fidelity and truthfulness of data can not be ascertained in every condition. A dead analysis is costly and is not viable to be used for all the conditions and cases as is required.
System preservation phase
System preservation phase would deal with preserving the evidence file and image of the target system. This would involve taking off the computer from the network and making a full copy of the hard drive image to get the whole data. This would reduce any chance of a malware or a spyware infecting and changing the data after preservation and hence all sorts of changes would result in a mismatch between the actual image and preserved image which would lead to disqualification of data image on grounds of data fidelity alone. Also, this prevents any overwrite in case of any changes being made to the data and changes would be reflected in the separate log which would be available and fidelity of the image file would be preserved. This process continues after data has been acquired from the system because we need to preserve the data for future analysis.
Preservation Techniques
The amount of overwriting still needs to be limited keeping up with storage costs available to the investigator. Therefore, evidence needs to be reduced to a certain amount of reduced processes that will be writing directly to the storage device. In the dead analysis, all processes are terminated first and then duplicate copies of data is made and written to the storage and write blockers are employed to prevent any case of overwriting and out of bound write occurring to the stored image. A live analysis would require suspect processes be killed or suspended. The network connection can be unplugged
and system be plugged into an empty hub or switch to prevent log messages about a dead link or network filters can be applied so that the perpetrator cannot connect from a remote system and delete data. Important data should be copied from the system in case it is overwritten while searching for evidence
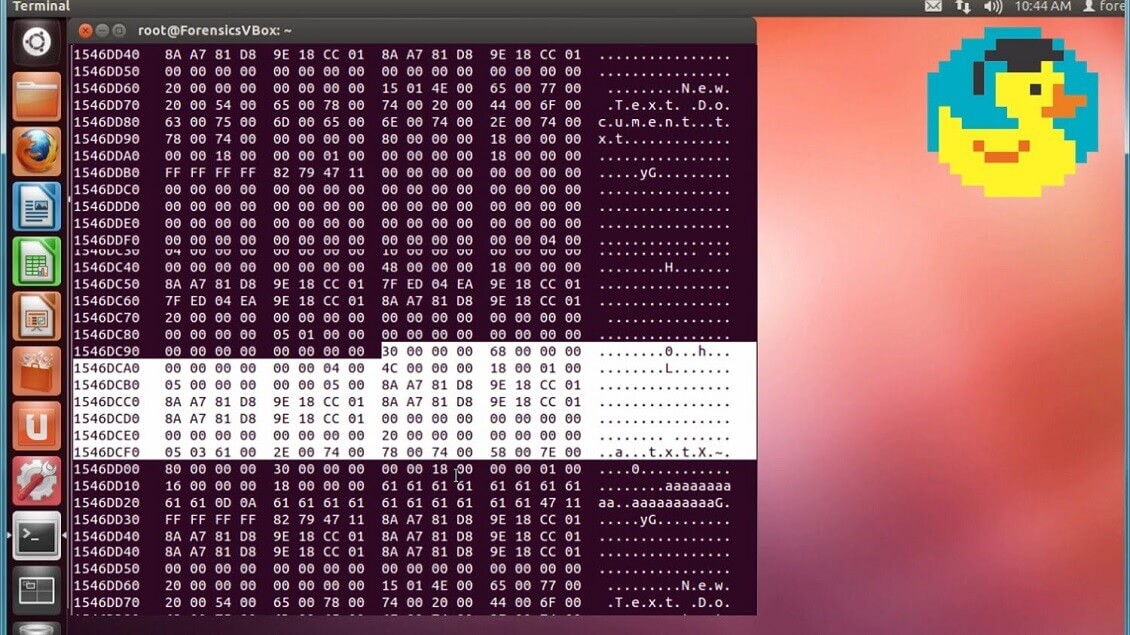
In maintaining the fidelity of data, a cryptographic checksum is generated in the form of MD5, SHA-1 for verification of the data. The checksum so generated is a very long string based on input characters which make up the image. Any change occurring after the generation of the checksum would lead to some changes in the checksum as well which would cause a mismatch in the generated checksum
When important data are saved during a dead or live analysis, a cryptographic hash should be calculated to later show that the data have not changed. A cryptographic hash, such as MD5, SHA-1, and SHA-256, is a mathematical formula that generates a very big number based on input data. These checksum algorithms are so designed such that it is extremely difficult to find two inputs that generate the same output. Therefore, if the hash value of your important data changes, then you know that the data has been modified.
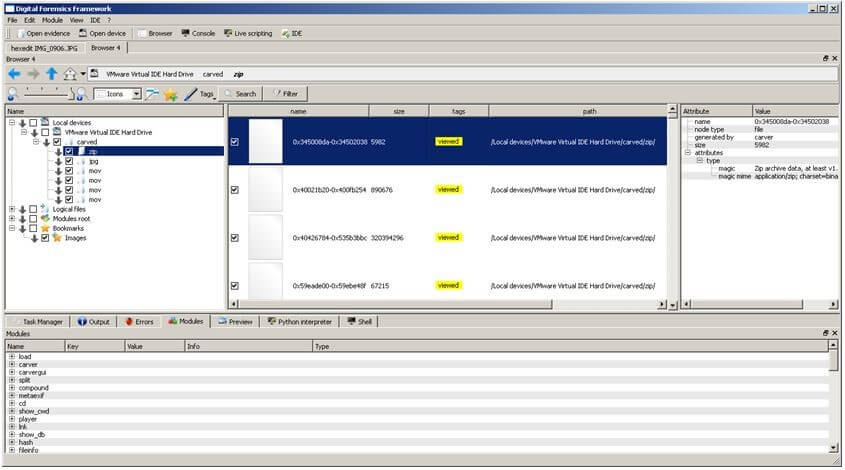
Evidence Searching Phase
Data preservation actively follows up with evidence searching phase. The process involves surveying data location around the MRU files and locations where the timeline of crime matches the timeline of the incident. This may start with a survey of common locations based on the type of incident if one is known. For example, if we are investigating Web-browsing habits, we will look at the Web browser cache, history file, and bookmarks as shown by the registry viewer under the most recently used registry changes in the changeLog. a Linux intrusion would consist of signs of a root-kit or new user accounts.evidence search would only act to confirm or refute the hypothesis formed by the initial reports about the crime.
Event Reconstruction Phase
The last phase of the investigation is to use the evidence that we found and determine what events occurred in the system. Our definition of an investigation was that we are trying to answer questions about digital events in the system. During the Evidence Searching Phase, we might have found several files that violate a corporate policy or law, but that does not answer questions about events. One of the files may have been the effect of an event that downloaded it, but we should also try to determine which application downloaded it. Is there evidence that a Web browser downloaded them, or could it be from malware? After the digital event reconstruction phase, we may be able to correlate the digital events with physical events. Event reconstruction requires knowledge about the applications and the OS that is installed on the system so that you can create hypotheses based on their capabilities.


